Since Windows Server 2008, we can use Group Policy Preferences to set a password for Local Administrator on all workstations in an OU. In May 2014, Microsoft released a patch to remove this feature. KB2962486
In fact, the password was stored insecurely. It was crypted using a key which is now public MSDN. This is a security leak, password are sent in “clear” and several time by day, using GPO application. If KB2928120 is installed on your system, you can’t no more use GPO to define password for:
- Drive Maps.
- Local Users.
- Scheduled Tasks.
- Services.
- Data Sources.
With the Security patch, Microsoft provided a Powershell script to change local password remotely.
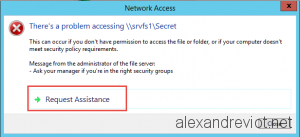
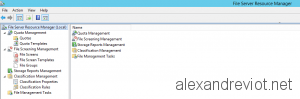
Since few days, Microsoft released a new tool: Local Administrator Password Solution (LAPS). With this tool, computers are able to randomly change password for local administrator and store it in Active Directory attribute.
Continue reading →