In order to reorganize an Active Directory forest, with multiple child domains into a single domain, I used the ADMT (Active Directory Migration Tool) 3.2 from Microsoft. This modification is an intraforest migration because all domains are in the same forest.
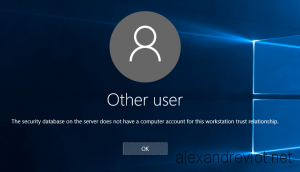
While ADMT supports an intraforest migration, I encountered a specific issue for migrated computers from a child domain to the parent domain: “The security database on the server does not have a computer account for this workstation trust relationship“
Well, I was very perplex by this error, because the ADMT agent reported an successfully operation, and the computer account existed in the new Active Directory domain.
In fact, you will get this error each time you want to migrate a computer with an intraforest and the target operating system is Windows Server 2012 R2. Let’s see why and how to resolve this issue.